- Right click on **RADIUS Clients**
- Click **New**, as shown in Figure [
Add New RADIUS Client](https://docs.netgate.com/pfsense/en/latest/recipes/radius-windows.html#figure-add-new-radius-client)
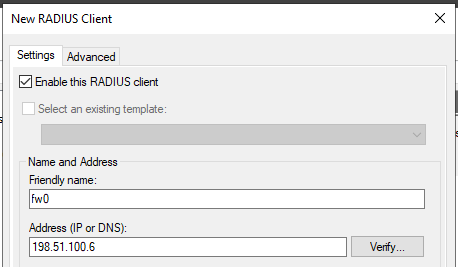
- Enter a **Friendly name** for the firewall, as shown in Figure [
Add New RADIUS Client Address](https://docs.netgate.com/pfsense/en/latest/recipes/radius-windows.html#figure-add-new-radius-client-address).
This can be the hostname or an FQDN.
- Enter the **Address (IP or DNS)** for the firewall.
This must be the IP address from which the firewall will initiate RADIUS requests or an FQDN which resolves to that IP address.
Note
This is the IP address of the firewall interface closest to the RADIUS server. If the RADIUS server is reachable via the firewall LAN interface, this will be the LAN IP address of the firewall. In deployments where the firewall is not the perimeter firewall, and the WAN interface resides on the internal network where the RADIUS server resides, the WAN IP address would be the correct address.