1. [Set the FSSO Collector Agent AD access mode](https://docs.fortinet.com/document/fortigate/7.2.9/administration-guide/795593#FSSO)
2. [Add an LDAP server](https://docs.fortinet.com/document/fortigate/7.2.9/administration-guide/795593#Add)
3. [Create the FSSO collector that updates the AD user groups list](https://docs.fortinet.com/document/fortigate/7.2.9/administration-guide/795593#Create)
4. [Use the AD user groups in a policy](https://docs.fortinet.com/document/fortigate/7.2.9/administration-guide/795593#Use)
1. Go to *User & Authentication > LDAP Servers*.
2. Click *Create New*.
3. Configure the settings as needed.
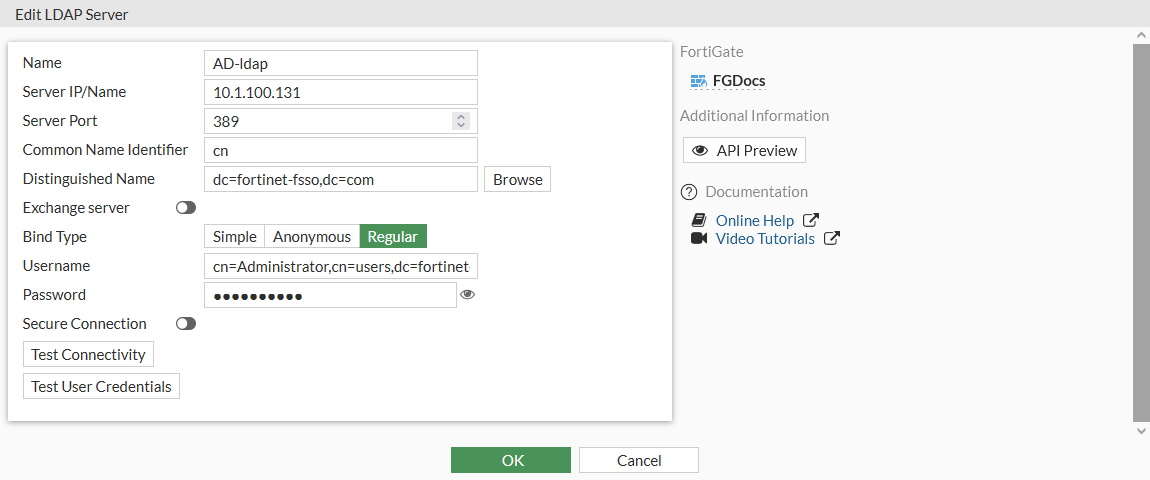
4. If secure communication over TLS is supported by the remote AD LDAP server:
1. Enable *Secure Connection* .
2. Select the protocol.
3. Select the certificate from the CA that issued the AD LDAP server certificate.
If the protocol is LDAPS, the port will automatically change to 636.
5. Click *OK*.
1. Go to *Security Fabric > External Connectors*.
2. Click *Create New*.
3. In the *Endpoint/Identity* section, click *FSSO Agent on Windows AD*.
4. Fill in the *Name*
5. Set the *Primary FSSO Agent* to the IP address of the FSSO Collector Agent, and enter its password.
6. Set the *User Group Source* to *Local*.
7. Set the *LDAP Server* to the just created *AD-ldap* server.
8. Enable *Proactively Retrieve from LDAP Server*.
9. Set the *Search Filter* to *(&(objectClass=group)(cn=group\*))*.
The default search filter retrieves all groups, including Microsoft system groups. In this example, the filter is configured to retrieve *group1*, *group2*, etc, and not groups like *grp199*.
The filter syntax is not automatically checked; if it is incorrect, the FortiGate might not retrieve any groups.
10. Set the *Interval (minutes)* to configure how often the FortiGate contacts the remote AD LDAP server to update the group information.
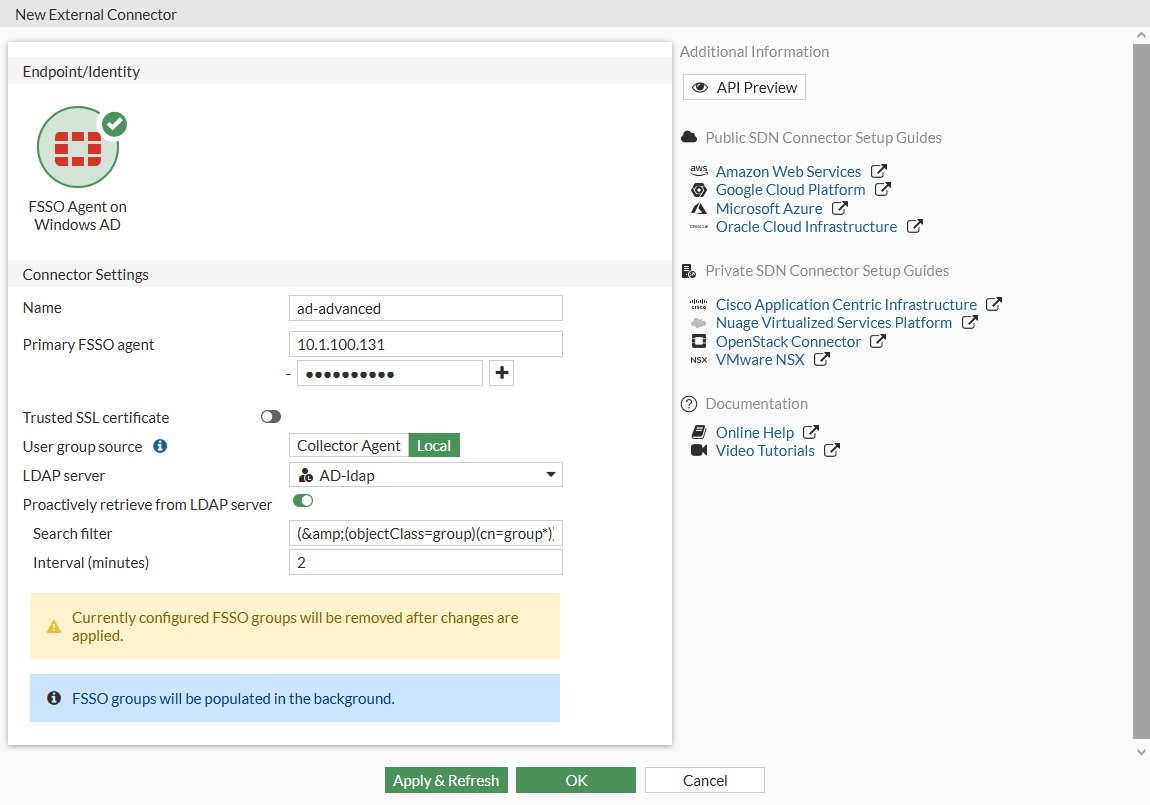
11. Click *OK*.
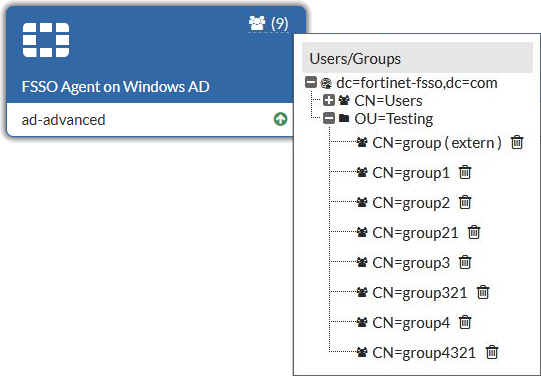
12. To view the AD user groups that are retrieved by the FSSO agent, hover the cursor over the group icon on the fabric connector listing.